Vendor Onboarding
Onboard Vendors. <strong>Eliminate Risk.</strong>
Use StackOne to connect your AI agent to your compliance, document management, and ticketing systems to automate vendor onboarding.
AI Agents
Connect
MCP and A2A to REST, SOAP, and proprietary APIs.
Optimize
Tool discovery, data shaping, and reliable execution.
Secure
Scoped permissions, audit trails, and observability.
StackOne Integration Layer
Connect
200+ connectors, build your own, and multi-protocol support.
Optimize
Context, token, and speed optimization infrastructure.
Secure
Permissions API and prompt injection protection.
What Can AI Agents Do for Vendor Onboarding?
Your agent orchestrates the entire onboarding pipeline — from document collection and sanctions screening to approval routing and stakeholder notification.
Collect Vendor Documents
Dispatch a digital onboarding form and collect W-9s, insurance certificates, banking details, and certifications. Store documents in SharePoint or Google Drive.
Screen for Compliance
Run the vendor against OFAC, EU sanctions, and denied-party watchlists. Verify insurance coverage and business licenses. Flag hits for human review.
Score and Classify Risk
Assign a risk tier based on screening results, geography, transaction volume, and industry. Auto-approve low-risk vendors; escalate medium and high-risk packages.
Route for Approval
Create approval tickets in Jira or ServiceNow for medium and high-risk vendors. Notify the compliance team via Slack or Gmail.
Notify and Schedule Re-certification
Confirm onboarding completion to stakeholders via Slack or Microsoft Teams and schedule periodic re-screening and annual re-certification.
Collect Vendor Documents
Dispatch a digital onboarding form and collect W-9s, insurance certificates, banking details, and certifications. Store documents in SharePoint or Google Drive.
Screen for Compliance
Run the vendor against OFAC, EU sanctions, and denied-party watchlists. Verify insurance coverage and business licenses. Flag hits for human review.
Score and Classify Risk
Assign a risk tier based on screening results, geography, transaction volume, and industry. Auto-approve low-risk vendors; escalate medium and high-risk packages.
Route for Approval
Create approval tickets in Jira or ServiceNow for medium and high-risk vendors. Notify the compliance team via Slack or Gmail.
Notify and Schedule Re-certification
Confirm onboarding completion to stakeholders via Slack or Microsoft Teams and schedule periodic re-screening and annual re-certification.
Why Building a Good Vendor Onboarding Agent Is Hard
Connecting Screening, Document, and Ticketing Systems
A vendor onboarding agent must read and write across compliance screening platforms, document storage, ticketing, and messaging — each with complex, proprietary APIs requiring separate connector builds and ongoing maintenance.
Auth Complexity Across Compliance Providers
Screening services, document platforms, and ticketing tools each demand different OAuth flows, API keys, and token refresh logic — multiplying auth maintenance per provider and per customer tenant.
Token Cost from Pre-Loading Action Definitions
Without search-first tool discovery, the agent must pre-load every action definition across screening, documents, ticketing, and messaging systems — burning tokens and increasing cost at scale before any onboarding work begins.
Vendor-Submitted Data Carries Prompt Injection Risk
Onboarding documents, W-9s, insurance certificates, and tax forms contain untrusted external content. Malicious or manipulated fields can alter agent behavior if passed directly to the LLM without a security layer.
How StackOne Makes Vendor Onboarding Agents Possible
Everything your vendor onboarding agent needs to collect documents, run compliance checks, and route approvals — with the controls procurement teams demand.
200+ connectors with 10K+ agent-optimized actions
Pre-built connectors for SharePoint, Google Drive, Jira, ServiceNow, Zendesk, Slack, and Gmail with full native action coverage and agent instructions included.
Managed Auth handles credentials across providers
OAuth flows, API keys, and token refresh managed per tenant for every connected screening, document, and ticketing provider — agents never touch raw credentials.
Search and execute finds the right action
Agent searches StackOne's action catalog by natural language and executes the matching action — no pre-loading thousands of tool definitions across screening, documents, and ticketing systems.
Managed Webhooks deliver onboarding events consistently
StackOne handles webhook registration and lifecycle across screening, document, and ticketing providers so the agent receives status updates — document uploads, screening completions, ticket approvals — without custom polling infrastructure.
Connector Studio extends to any system
Build custom connectors for niche compliance screening tools or procurement platforms via REST, SOAP, or GraphQL — extend agent reach without maintaining bespoke integration code.
Defender blocks prompt injection from vendor documents
StackOne Defender screens untrusted vendor-submitted content — W-9s, onboarding forms, insurance certificates — before the agent processes it, preventing adversarial content from manipulating onboarding behavior.
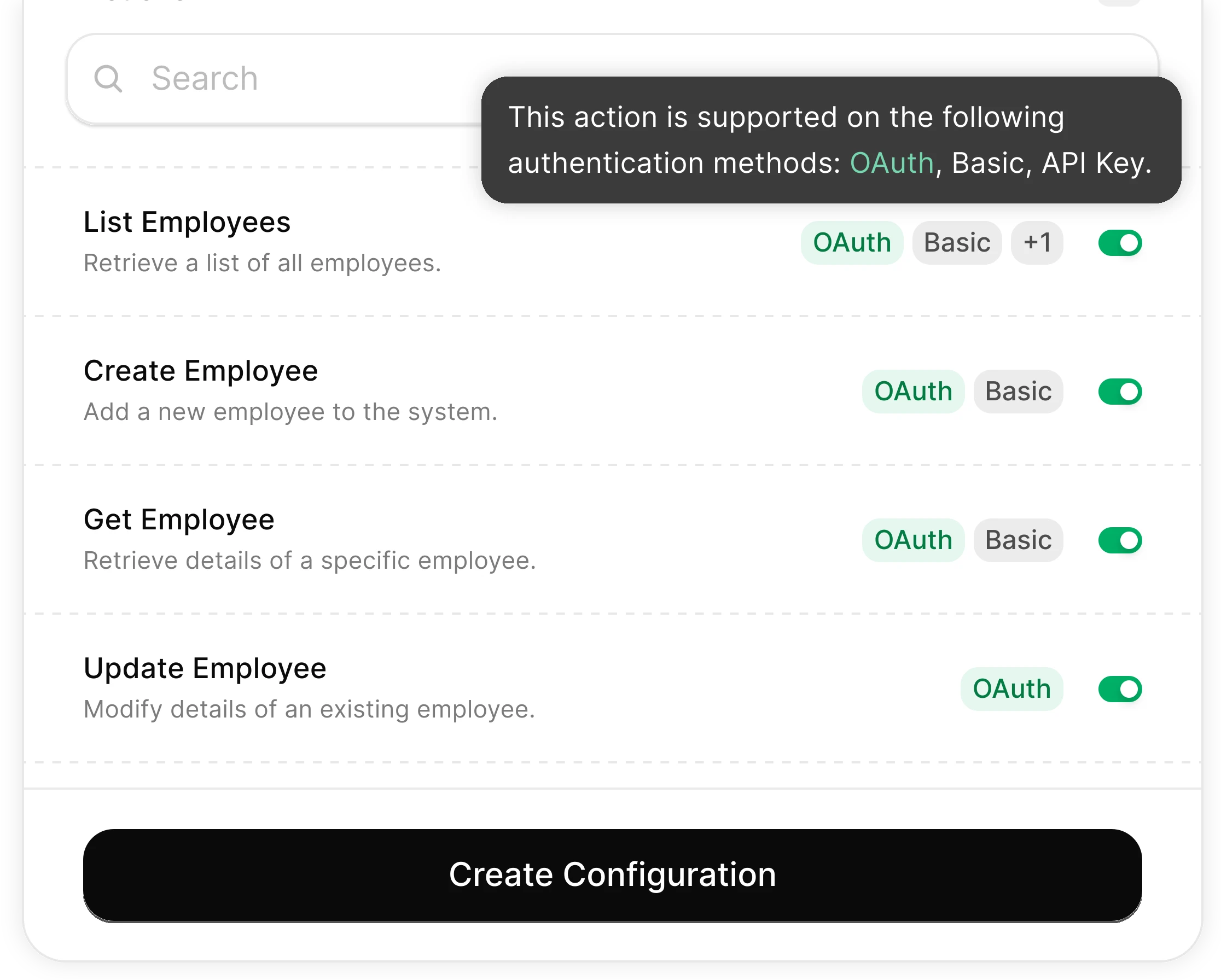
You Control What the Agent Can Do
Scoped permissions define exactly which documents the agent reads and which onboarding actions it can trigger. Full audit trail of every screening decision and approval action.
Integrates with your entire procurement stack. Whatever it is.
Connect Any Agent to Automate Vendor Onboarding
Any Agent Framework
Claude, OpenAI, LangChain, Vercel AI SDK, CrewAI, Pydantic AI — StackOne works with every major agent framework out of the box.
Any Agent Builder
Whether you're building with code, a visual builder, or an enterprise platform — StackOne provides the integration layer your agent needs.
Connect Your Agent to Your Procurement Stack
Start building in minutes. MCP connectors to every system your agent needs.
Frequently Asked Questions
Connect Your Agent to Your Procurement Stack
Start building in minutes. MCP connectors to every system your agent needs.