Employee Offboarding
Offboard Without the Risk
Use StackOne to connect your AI agent to your HRIS, identity management, and ITSM to automate employee offboarding and deprovisioning.
AI Agents
Connect
MCP and A2A to REST, SOAP, and proprietary APIs.
Optimize
Tool discovery, data shaping, and reliable execution.
Secure
Scoped permissions, audit trails, and observability.
StackOne Integration Layer
Connect
200+ connectors, build your own, and multi-protocol support.
Optimize
Context, token, and speed optimization infrastructure.
Secure
Permissions API and prompt injection protection.
What Can AI Agents Do for Employee Offboarding?
Your agent detects termination events, orchestrates access revocation across every system, processes final pay, and closes the offboarding case with a full audit trail.
Notify Stakeholders
Send a structured offboarding timeline and task assignments to the manager, HR, and IT via Slack or email. Include knowledge transfer deadlines and equipment return instructions.
Audit Access & Transfer Knowledge
Pull a full inventory of the departing employee's system access from Okta or the identity provider. Identify owned documents in Google Drive or SharePoint for reassignment.
Revoke Access Across Systems
On the termination date, execute coordinated deprovisioning: disable SSO, revoke tokens, remove SaaS access via the identity provider, and deactivate the employee record in the HRIS.
Process Final Pay
Confirm final paycheck details — PTO payout, severance, expense reimbursements — within the HRIS where payroll is embedded. Flag COBRA and benefits continuation notices for manual processing.
Verify & Close
Run a final audit confirming all access revoked, equipment returned, and records archived. Close the offboarding case in Jira or ServiceNow.
Detect Termination Events
Monitor resignation or termination events from Workday, BambooHR, or Personio. Create an offboarding case in ITSM with employee details and last working day.
Notify Stakeholders
Send a structured offboarding timeline and task assignments to the manager, HR, and IT via Slack or email. Include knowledge transfer deadlines and equipment return instructions.
Audit Access & Transfer Knowledge
Pull a full inventory of the departing employee's system access from Okta or the identity provider. Identify owned documents in Google Drive or SharePoint for reassignment.
Revoke Access Across Systems
On the termination date, execute coordinated deprovisioning: disable SSO, revoke tokens, remove SaaS access via the identity provider, and deactivate the employee record in the HRIS.
Process Final Pay
Confirm final paycheck details — PTO payout, severance, expense reimbursements — within the HRIS where payroll is embedded. Flag COBRA and benefits continuation notices for manual processing.
Verify & Close
Run a final audit confirming all access revoked, equipment returned, and records archived. Close the offboarding case in Jira or ServiceNow.
Why Building a Good Employee Offboarding Agent Is Hard
Connecting HRIS, IAM, and ITSM Systems
The agent needs connectors to Workday, BambooHR, Personio, Okta, Azure AD, ServiceNow, and more. Building each one — auth flows, pagination, rate limits — is a massive lift that multiplies with every customer environment.
Multi-Provider Auth in Hybrid IAM Environments
Each identity provider — Okta, Azure AD, Google Workspace — has different OAuth flows, token formats, and permission scopes. The agent must store and refresh credentials per tenant without mixing contexts, across every provider combination.
Token Cost and Tool Discovery at Scale
Without search-first architecture, the agent pre-loads every action definition across HRIS, IAM, and ITSM systems into its context window, burning tokens and money on irrelevant tools before deprovisioning even starts.
Prompt Injection via Employee Data Fields
Offboarding agents ingest names, manager notes, and free-text fields from HRIS records. Malicious content embedded in those fields can hijack agent behavior during deprovisioning — for example, injecting instructions to skip access revocation.
How StackOne Makes Employee Offboarding Agents Possible
Everything your offboarding agent needs to detect terminations, revoke access, and close cases — with the controls IT and compliance demand.
200+ connectors with 10K+ agent-optimized actions
Pre-built connectors for Workday, BambooHR, Personio, Okta, Azure AD, ServiceNow, and Slack with full native action coverage and agent instructions included.
Managed Auth handles credentials across providers
OAuth flows, API keys, and token refresh managed per tenant for every connected HRIS and identity provider — agents never touch raw credentials.
Search and execute finds the right action
Agent searches StackOne's action catalog by natural language and executes the matching HRIS or IAM action — no pre-loading thousands of tool definitions.
Managed Webhooks deliver termination events consistently
StackOne subscribes to HRIS termination events across all providers through one webhook layer — includes retry logic and synthetic polling for systems lacking native webhooks.
Connector Studio extends to any system
Build custom connectors for unsupported IAM providers or internal deprovisioning systems via REST, SOAP, or GraphQL — no waiting on vendor support.
Defender blocks prompt injection from employee data
StackOne Defender screens inbound HRIS fields — names, notes, free-text descriptions — for injection attempts before the agent processes them, preventing adversarial content from manipulating deprovisioning behavior.
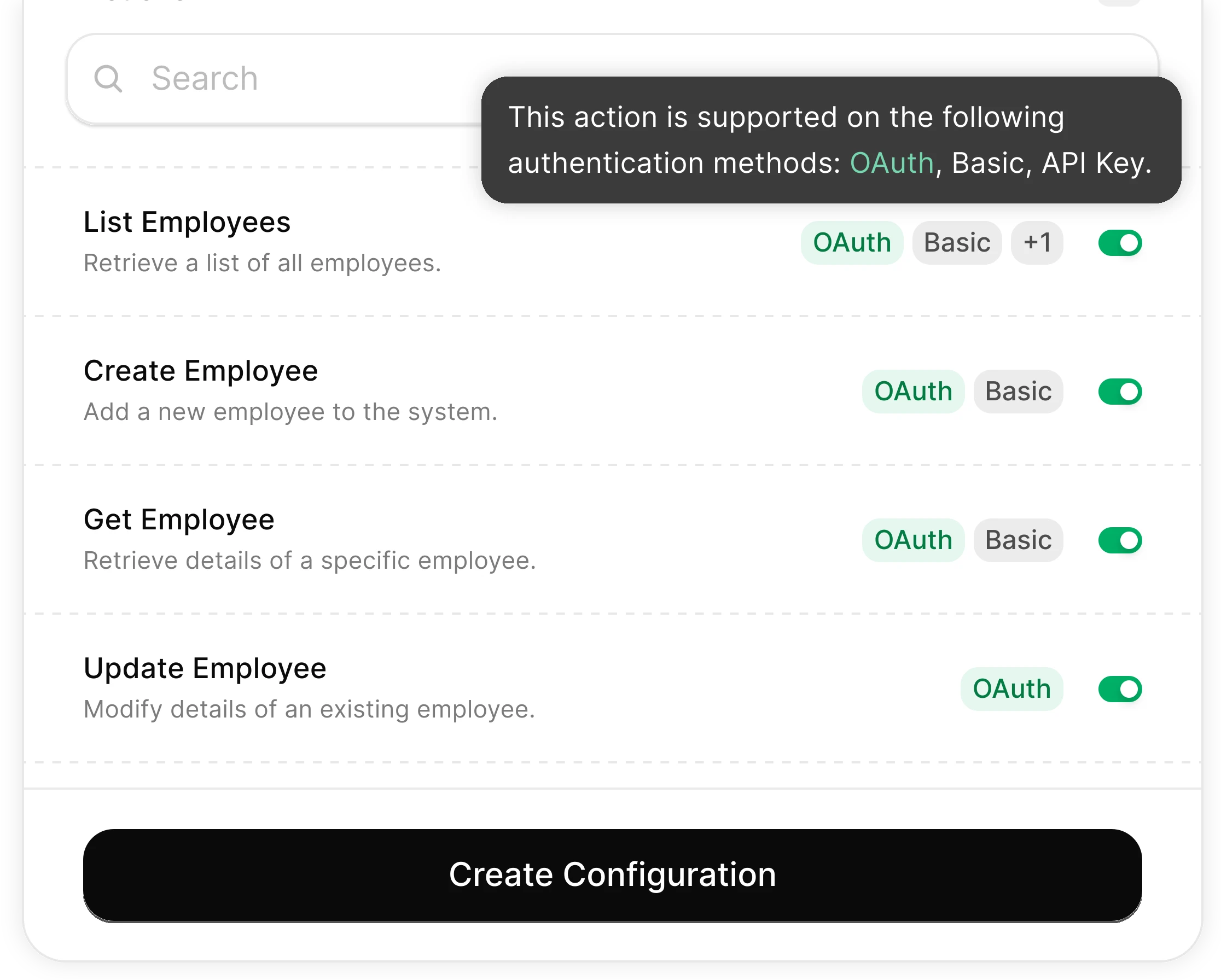
You Control What the Agent Can Do
Scoped permissions define exactly which employee data the agent reads and which deprovisioning actions it can trigger. Full audit trail of every operation for SOC 2 and ISO 27001 compliance.
Integrates with your entire HR and IT stack. Whatever it is.
Connect Any Agent to Automate Employee Offboarding
Any Agent Framework
Claude, OpenAI, LangChain, Vercel AI SDK, CrewAI, Pydantic AI — StackOne works with every major agent framework out of the box.
Any Agent Builder
Whether you're building with code, a visual builder, or an enterprise platform — StackOne provides the integration layer your agent needs.
Connect Your Agent to Your HR and IT Stack
Start building in minutes. MCP connectors to every system your agent needs.
Frequently Asked Questions
Connect Your Agent to Your HR and IT Stack
Start building in minutes. MCP connectors to every system your agent needs.